# MikroTik-RouterOS-7.16.1永久L6授权 (支持各种ESXI PVE 2.5G i225,6RTL8125网卡直通-软路由,x86系统,openwrt(x86),Router OS 等-恩山无线论坛
---
全网唯一!!!!!!下载下来如果不是最新版,联网后可以在线升级到最新版。
同时支持intel i225、i226 和
Realtek RTL8125(ROS7.15版本开始支持)的2.5G网卡并使用UEFI引导的RouterOS破jie系统基于UEFI引导的MikroTik-RouterOS 虚拟机镜像,L6永久授权,可升级,
支持IPV6和100G网卡直通使用
支持DD写在硬盘上安装在实体机上使用前排提醒:
RouterOS配置好能正常上网之后一定要做好安全策略!!!!!!
RouterOS配置好能正常上网之后一定要做好安全策略!!!!!!
RouterOS配置好能正常上网之后一定要做好安全策略!!!!!!

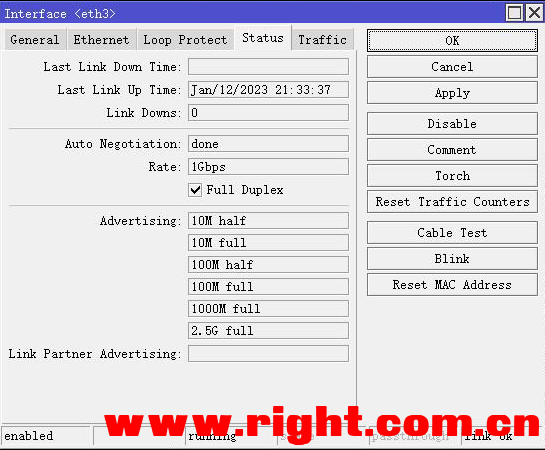
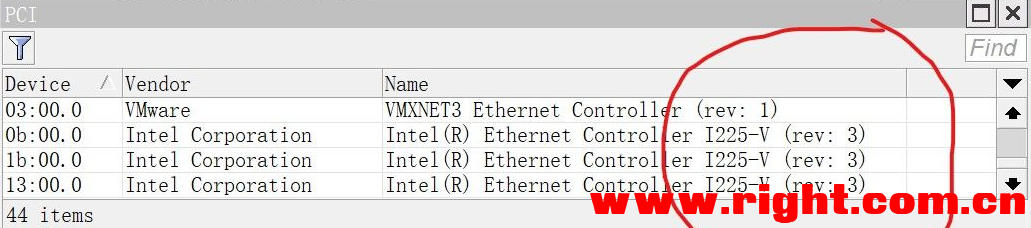
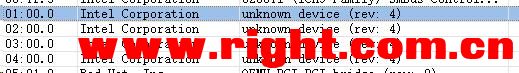
intel i225直通后可以正常显示网卡名称,intel i226直通后显示为未知设备(不影响使用)
虚拟硬盘空间6GB,支持大内存
默认用户名为 admin 密码为空。
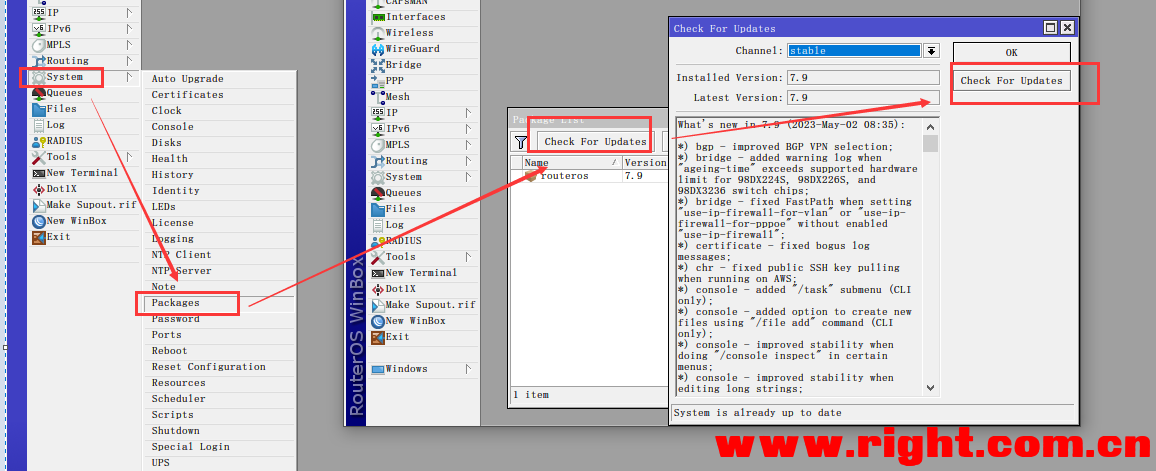
MikroTik-RouterOS官方版本默认进去就是没有密码,要输入密码进去的小心后门本镜像为完整包,WinBox进入System→Packages可以根据自己需求关闭或者卸载不需要的功能包,重启后生效。
\<\<\<其中routeros包为核心包,禁止卸载或者禁用\>\>\>
-----------------------------------------------------------------
安装RouterOS的CPU建议选择 高主频 intel,搭配intel网卡使用有加成,
ROS对多核心多线程优化不太好,超线程建议在BIOS中关闭,对于大小核心的CPU建议只使用大核心。
(PS:AMD的CPU+intel网卡做软路由可能会出现1核有难其余围观的情况)推荐使用的RouterOS直通网卡支持列表:(建议优先使用intel原装或服务器拆机网卡,不要使用寨卡和部分厂商的OEM卡,ROS对于BCM网卡的兼容性不太好)
1G intel i210 i350 等
2.5G intel i225 i226 + Realtek RTL8125(ROS7.15版本开始支持)
10G intel X520 X540 X550 X710 X722等
25G intel XXV710 E810 等
40G intel XL710
100G intel E810、Mellanox CX516A、CX515A 、Chelsio T62100-SO-CR 必须设置为Ethernet模式,不支持Infiband模式
RouterOS 7.12版本起支持Mellanox ConnectX-6 Dx 100G网卡
---
下载链接:
关于如何使用在附件中已经写的很清楚了支持在线升级,检查更新后会自动安装更新,
无需每次升级后都要下载网盘的附件重新配置路由
关于如何使用在附件中已经写的很清楚了
支持ESXI, PVE, UNRAID
L6永久授权,可以随意升级,不可以降级到ROS6,旧系统不支持uefi引导
pve虚拟机可能由于版本不同,操作有不同,但是改配置文件是必须要做的
可以参加这个帖子https://www.right.com.cn/forum/thread-7951255-1-1.html
或者参考71#庄生夢蝶㊣贴出来的图片版本设置,注意bios一定要改成uefi模式
https://www.right.com.cn/forum/f ... 271574&pid=18078752
unraid和pve一样都是kvm虚拟机,能修改磁盘配置文件,加后面的那段磁盘序列号,也是可以用的,拉到最后在</domain>上面添加下面代码
可以参考这个https://www.right.com.cn/forum/thread-8263856-1-1.html
ros无需每次都下载破解版的,可以在线更新的,方法如下图
RouterOS 默认防火墙规则
Mikrotik 的官方硬件产品默认都有带有配置良好的防火墙规则,x86/CHR 设备默认不带防火墙规则。 如果你不小心删掉了防火墙规则,或者需要还原默认防火墙规则,可以导入以下配置(不要照抄,根据实际情况修改后使用):
/interface list
add comment=defconf name=WAN
add comment=defconf name=LAN
/interface list member
add comment=defconf interface=bridge list=LAN
add comment=defconf interface=ether1 list=WAN
/ip firewall filter
add action=accept chain=input comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=invalid
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment="defconf: accept to local loopback (for CAPsMAN)" dst-address=127.0.0.1
add action=drop chain=input comment="defconf: drop all not coming from LAN" in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept in ipsec policy" ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" connection-state=established,related hw-offload=yes
add action=accept chain=forward comment="defconf: accept established,related, untracked" connection-state=established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" connection-state=invalid
add action=drop chain=forward comment="defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat connection-state=new in-interface-list=WAN
/ipv6 firewall address-list
add address=::/128 comment="defconf: unspecified address" list=bad_ipv6
add address=::1/128 comment="defconf: lo" list=bad_ipv6
add address=fec0::/10 comment="defconf: site-local" list=bad_ipv6
add address=::ffff:0.0.0.0/96 comment="defconf: ipv4-mapped" list=bad_ipv6
add address=::/96 comment="defconf: ipv4 compat" list=bad_ipv6
add address=100::/64 comment="defconf: discard only " list=bad_ipv6
add address=2001:db8::/32 comment="defconf: documentation" list=bad_ipv6
add address=2001:10::/28 comment="defconf: ORCHID" list=bad_ipv6
add address=3ffe::/16 comment="defconf: 6bone" list=bad_ipv6
/ipv6 firewall filter
add action=accept chain=input comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=invalid
add action=accept chain=input comment="defconf: accept ICMPv6" protocol=icmpv6
add action=accept chain=input comment="defconf: accept UDP traceroute" port=33434-33534 protocol=udp
add action=accept chain=input comment="defconf: accept DHCPv6-Client prefix delegation." dst-port=546 protocol=udp src-address=fe80::/10
add action=accept chain=input comment="defconf: accept IKE" dst-port=500,4500 protocol=udp
add action=accept chain=input comment="defconf: accept ipsec AH" protocol=ipsec-ah
add action=accept chain=input comment="defconf: accept ipsec ESP" protocol=ipsec-esp
add action=accept chain=input comment="defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=input comment="defconf: drop everything else not coming from LAN" in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" connection-state=invalid
add action=drop chain=forward comment="defconf: drop packets with bad src ipv6" src-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: drop packets with bad dst ipv6" dst-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: rfc4890 drop hop-limit=1" hop-limit=equal:1 protocol=icmpv6
add action=accept chain=forward comment="defconf: accept ICMPv6" protocol=icmpv6
add action=accept chain=forward comment="defconf: accept HIP" protocol=139
add action=accept chain=forward comment="defconf: accept IKE" dst-port=500,4500 protocol=udp
add action=accept chain=forward comment="defconf: accept ipsec AH" protocol=ipsec-ah
add action=accept chain=forward comment="defconf: accept ipsec ESP" protocol=ipsec-esp
add action=accept chain=forward comment="defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=forward comment="defconf: drop everything else not coming from LAN" in-interface-list=!LAN

评论区